Vancouver IT Company Discusses How Misconfigurations Create Cyber Risks for Modern Business Systems
Vancouver, United States – March 27, 2026 / Computers Made Easy – Vancouver Managed IT Services Company /
IT Company in Vancouver Highlights Hidden Risks of Security Misconfigurations
In 2025, configuration mistakes sat at the center of 82% of cloud-related compromises, leaving sensitive data exposed.
As Danny Tehrani, President/Founder at Computers Made Easy, explains: “A business can only protect what it clearly understands. Security gaps are invisible until they cost you.”
Security misconfiguration sits at the center of modern cyber risk. Small and mid sized businesses move fast, focus on growth, and rely on lean IT teams. That pace creates small but dangerous cracks inside systems, applications, and cloud environments.
A single overlooked setting can open a path for attackers, and most organizations never see the gap until it becomes a breach.
Misconfiguration happens when essential controls are missing or when systems are set up incorrectly. Cloud platforms, firewalls, identity tools, and SaaS applications all carry configuration requirements. Each requirement represents a safeguard. When those safeguards fall out of alignment, the business carries silent exposure.
The impact grows quickly for SMBs. Limited staffing, rapid cloud adoption, and third party integrations create an environment where misconfigurations spread across multiple systems.
Downtime, data exposure, and financial loss follow. Every day a misconfigured system stays active, the probability of an attack increases. These risks become clear when you look at the core areas where misconfiguration creates business exposure:
-
Access control gaps: Permissions expand quietly and give users or attackers more reach than intended.
-
Cloud setup errors: Storage buckets, virtual machines, and services run without proper restrictions.
-
Unpatched components: Default settings remain unchanged and create predictable entry points.
-
Logging blind spots: Critical events go unmonitored, leaving teams unaware of active threats.
Recognizing these risks is the first step toward stronger protection. Addressing misconfiguration strengthens business continuity, protects sensitive information, and preserves customer trust. A secure configuration becomes a foundation for resilience, not an afterthought.
In this article, a reliable Vancouver IT firm explains what security misconfiguration is, how it creates vulnerabilities, and what businesses can do to reduce these risks.
How to Prevent Security Misconfiguration Attacks
Prevention creates stability. SMBs gain stronger protection when they apply consistent controls across systems, applications, and cloud environments. These actions build a secure foundation that supports growth and reduces operational risk:
-
Regular patching: Updates close known vulnerabilities and keep systems resilient against active threats.
-
Strong access controls: Users receive only the access required for their roles. Authentication policies and log reviews maintain visibility and accountability.
-
Secure coding standards: Developers validate inputs, encode outputs, and manage errors with care. Security built into development prevents application level misconfigurations.
-
Cloud configuration reviews: Routine audits of permissions, access rules, and storage settings close gaps inside cloud platforms.
-
Continuous monitoring: Real time alerts highlight unusual activity and configuration changes, giving teams the ability to respond quickly.
Preventive strategies protect data, maintain business continuity, and support confident growth. Strong controls create an environment where security becomes a natural part of daily operations.
Diagnosing and Fixing Security Misconfigurations
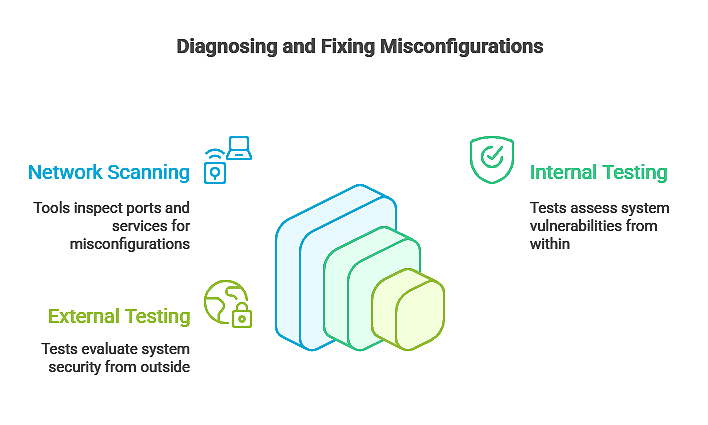
Verification strengthens every security program. Preventive measures create stability, but diagnosis confirms that systems remain aligned with security standards.
A structured approach to detection reveals hidden weaknesses and keeps your environment resilient. These diagnostic practices create clarity and control:
-
Security audits: Comprehensive reviews uncover configuration gaps across systems and applications. Audits validate settings, confirm compliance with security requirements, and highlight areas that need immediate attention.
-
Network scanning: Scanning tools inspect ports, services, and endpoints to reveal misconfigurations. Regular scans provide visibility into weaknesses that stay hidden during daily operations.
-
Internal and external testing: Penetration testing shows how attackers might exploit misconfigurations. Testing before deployment strengthens defenses and reduces exposure across production environments.
Fast detection keeps small issues from escalating into costly incidents. Diagnosis builds confidence in your IT environment and supports continuous protection. Regular reviews create a security posture that stays aligned with business needs and operational demands.
Real World Consequences of Security Misconfigurations
Security misconfigurations have moved far beyond theory. They have triggered breaches with measurable impact, proving that even small oversights can create massive exposure. These incidents highlight how attackers exploit misaligned settings and how quickly the fallout spreads across industries:
1. Default credentials
Publicly documented usernames and passwords give attackers instant access. In 2021, Nissan North America exposed internal mobile app source code because a default Git server password remained active. FOUNDATION Software faced a similar issue in 2024 when hackers brute forced 33 publicly accessible hosts, compromising accounting data across construction firms.
2. Cloud misconfigurations
Misaligned cloud storage permissions create large scale leaks. In January 2023, T Mobile’s misconfigured S3 bucket exposed data for more than 30 million customers.
3. Firewall misalignment
Capital One’s 2019 breach affected nearly 100 million U.S. and Canadian customers after a misconfigured web application firewall gave attackers access to sensitive financial records. The incident resulted in an 80 million dollar regulatory fine and a 190 million dollar class action settlement.
4. Public data settings
Microsoft Power Apps exposed 38 million records in 2021 because default public settings remained active. Organizations such as American Airlines and Ford were directly affected.
These examples show how misconfigurations translate into financial loss, operational disruption, and reputational damage. Unauthorized access, stolen data, and regulatory penalties are not abstract risks but tangible outcomes. For SMBs, even minor misconfigurations can escalate quickly, making proactive audits and continuous configuration management essential to protecting digital assets and maintaining trust.
Security Misconfiguration Quick-Check for SMBs
Below is a practical reference for SMB IT teams. It identifies common misconfigurations, their impact, and the first remediation step.
|
Misconfiguration Type |
Potential Impact |
First Step to Fix |
|
Default Credentials |
Unauthorized access |
Change all default passwords immediately |
|
Unpatched Systems |
Exploitable vulnerabilities |
Apply latest security patches |
|
Cloud Misconfigurations |
Data exposure |
Audit cloud storage permissions |
|
Web Server Errors |
Application compromise |
Remove default/sample files and enforce SSL |
|
Identity Access Misconfiguration |
Unauthorized modifications |
Review and limit user permissions |
|
Disabled Antivirus |
Malware infections |
Enable and update antivirus software |
Use this table as a starting checklist. It provides actionable insight for IT teams to identify risks quickly. Addressing these issues promptly reduces exposure and strengthens your security posture.
Secure Your IT with a Trusted IT Firm in Vancouver
Security misconfiguration is more than a technical phrase. It is a daily risk for SMBs, creating openings that attackers exploit. From default passwords to cloud gaps, these vulnerabilities weaken defenses and expose sensitive data. Recognizing misconfiguration examples, diagnosing weaknesses, and applying preventive measures builds resilience across your IT environment.
Computers Made Easy delivers proactive IT management, monitoring, and cybersecurity support.
With over 27 years of experience and a team of 18+ certified technicians, CME identifies misconfigurations quickly and resolves them before they escalate. Our expertise ensures your systems remain secure, compliant, and reliable.
Partnering with CME gives your business immediate advantages:
-
Proactive monitoring: Continuous oversight detects misconfigurations before they become threats.
-
Expert remediation: Certified technicians apply fixes that strengthen system reliability.
-
Cyber resilience: Integrated security practices protect data and maintain business continuity.
-
Trusted experience: Decades of service provide confidence that your IT environment is secure.
Contact a trusted IT firm in Vancouver today to identify hidden configuration risks and strengthen your security posture.

Contact Information:
Computers Made Easy – Vancouver Managed IT Services Company
7710 NE Greenwood Dr Suite 230
Vancouver, WA 98662
United States
Danny Tehrani
(888) 565-4954
https://www.computersmadeeasy.com/
Original Source: https://www.computersmadeeasy.com/what-is-a-security-misconfiguration/
